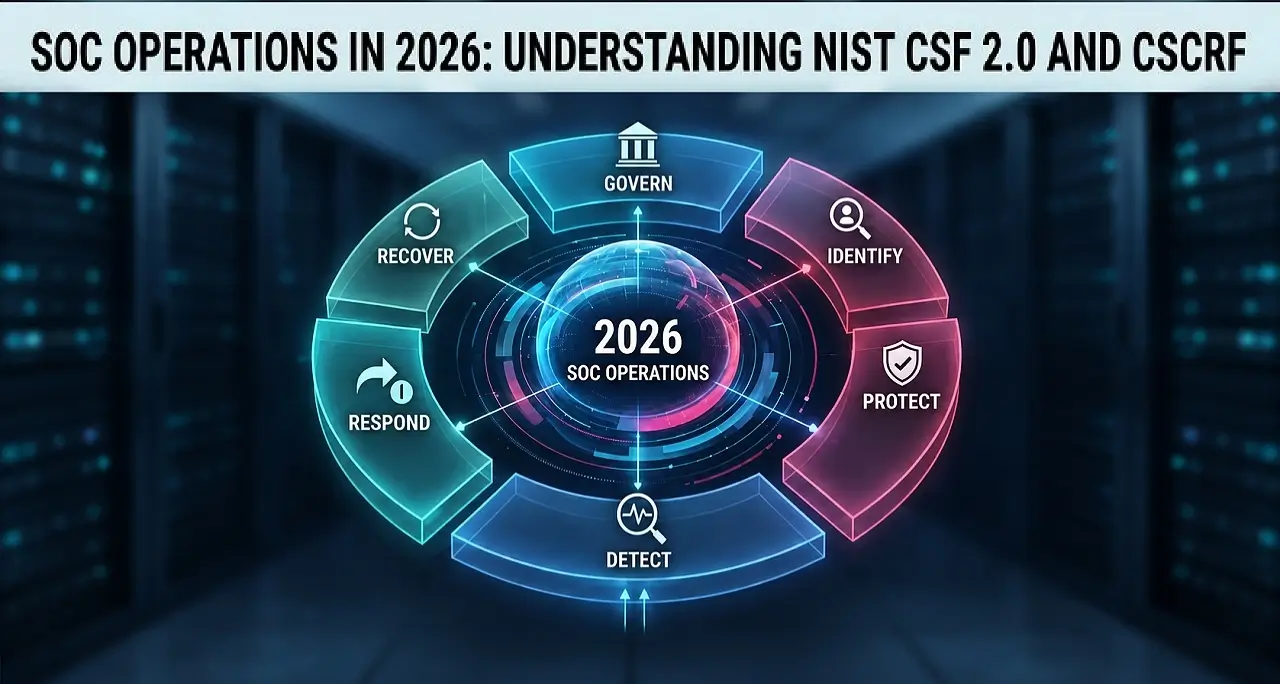
SOC Operations in 2026: Understanding NIST CSF 2.0 and CSCRF
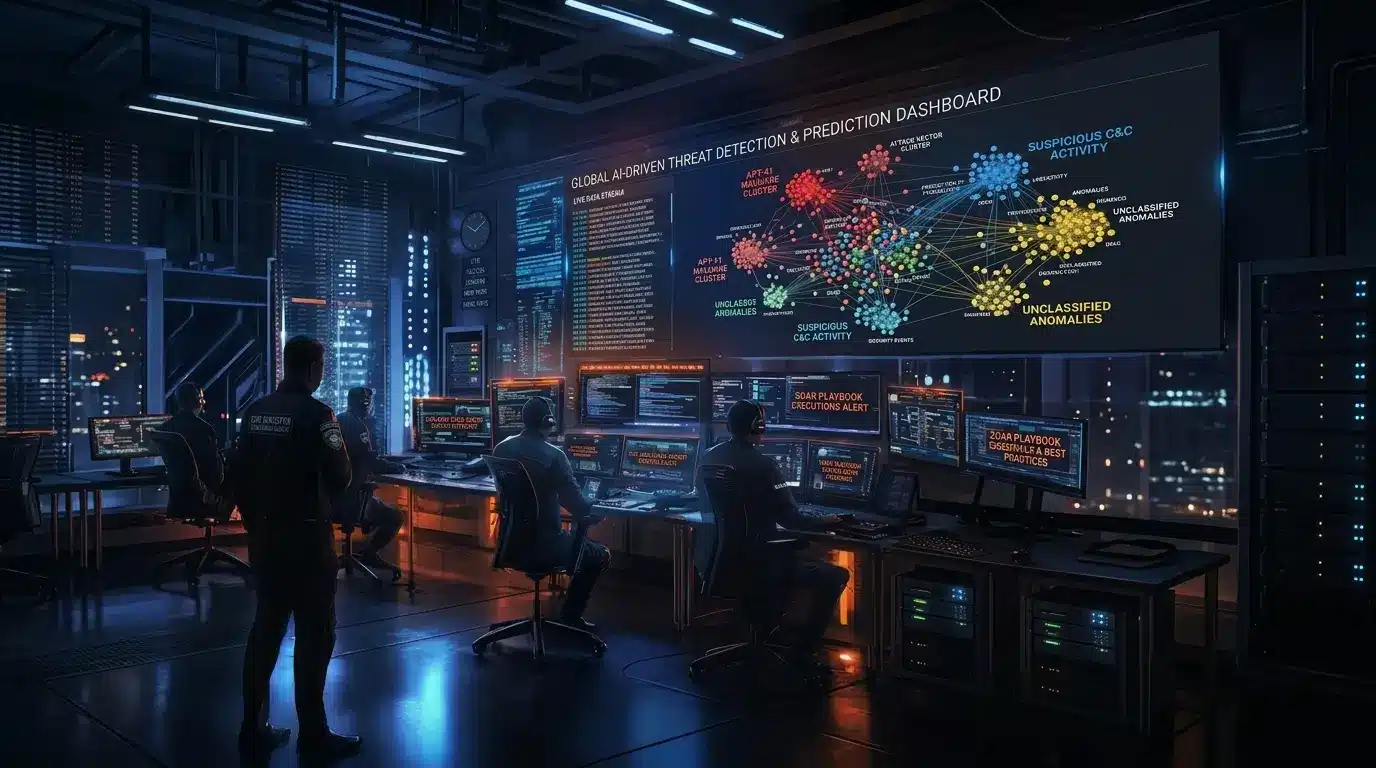
Why Modern SOCs Need Frameworks In 2026, modern Security Operations Centers (SOCs) operate across hybrid cloud infrastructure, SaaS platforms, distributed identities, APIs, and increasingly complex regulatory environments. Many organizations deploy advanced technologies such as SIEM, XDR, threat intelligence, and cloud-native analytics platforms, and yet struggle with alert fatigue, inconsistent detection…