Cyber risk is defined by asymmetry: Attackers need one entry point, while organisations must defend an expanding digital estate across cloud, endpoints, applications, and third parties. More than 80% of breaches begin with low friction vectors such as phishing, where a single compromised credential can escalate into a broader intrusion. At the same time, security teams face a different challenge: volume. Modern environments generate vast telemetry, but critical signals are often lost in noise.
The challenge is no longer prevention alone, but the ability to detect, prioritise, and respond to threats quickly enough to limit impact. This blog examines how organisations structure security operations to address this challenge, and the role a Security Operations Center (SOC) plays within that model.
What is a Security Operations Center (SOC)?
A SOC is a centralised function responsible for continuously monitoring, detecting, and responding to cyber threats across an organisation’s environment. It integrates people, processes, and technology to maintain real-time visibility and coordinated defence. Rather than relying on isolated security tools, a SOC operates as a control layer, correlating data from networks, endpoints, cloud platforms, and applications to identify and support timely response. It enables organisations to move from fragmented monitoring to structured, response-driven security operations.
Why Organisations Need a SOC
The need for a SOC is driven by structural changes in how modern environments are built and attacked.
- Expanding attack surface: Cloud adoption, distributed workforces, and connected devices have significantly increased the number of potential entry points. Without centralised oversight, organisations operate with gaps in visibility that can be exploited by attackers.
- Data overload: Security tools generate large volumes of telemetry flow, but without effective correlation, critical signals are often lost. A SOC helps convert this data into actionable insight.
- Operational fatigue: Security teams face a constant stream of alerts, many of which are false positives. This reduces analyst effectiveness and increases the likelihood that genuine threats are overlooked. Structured triage and automation help manage this load.
- Delayed detection: In the absence of continuous monitoring, attackers can remain undetected for extended periods.
- Time-critical decisions: Cyber incidents require fast, informed decision-making. Centralised visibility and context improve the ability to respond effectively under pressure.
- Quantifying SOC Value: Metrics that Matter The value of a SOC is reflected in how effectively it limits the scale, duration, and cost of security incidents. The data below highlights how these factors translate into measurable outcomes across global and Indian organisations.
Quantifying SOC Value: Metrics that Matter
The value of a SOC is reflected in how effectively it limits the scale, duration, and cost of security incidents. The data below highlights how these factors translate into measurable outcomes across global and Indian organisations.
Global vs Indian SOC Metrics
| Metric | Global | India | Explanation/Notes | Source |
| Average cost of a data breach | ₹36.8 crore | ₹22 crore | Global cost declined slightly in 2025 while India reached its highest recorded level (+13%YoY). | IBM Cost of a Data Breach Report 2025 |
| Breach lifecycle (identification + containment) | 241 days | 263 days | India has improved year-on-year but still exceeds the global average | IBM 2025 Report |
| Cost savings from AI & automation | ~₹15–18 crore | ~₹13 crore | AI and automation reduce both breach cost and lifecycle duration. | IBM/Ponemon 2024–2025 |
| Organizations planning a SOC | ~50% of large firms | ~44% of large Indian firms | These numbers are based on survey intent, not actual SOC deployments. | Kaspersky 2026 (survey-based) |
| Incidents / breaches reported | 6,000+ breaches studied | ~1.39 million incidents reported | Global figure reflects analysed breaches; India figure includes all reported incidents, most of which are of lower severity. | IBM/Ponemon; ERT- n Report 2022 |
Key Insights
- Detection speed influences breach cost.
Faster detection and containment materially reduce breach costs. In India, incidents contained within 200 days cost significantly less than those that persist longer. - Detection is increasingly internal.
A growing proportion of intrusions are identified internally, reflecting increased reliance on SOC capabilities rather than external notification. - Automation improves outcomes.
Organisations using AI and automation shorten breach lifecycles and reduce overall incident costs. - India lags global benchmarks.
Longer breach lifecycles in India indicate slower identification and containment, highlighting a gap in operational maturity. - Integrated tooling improves efficiency.
Tool consolidation and integrated detection improve analyst efficiency, reduce false positives, and deliver strong return on investment.
These metrics show that breach outcomes are largely shaped by how effectively organisations identify, prioritise, and contain threats. Faster containment reduces the risk of escalation and limits overall business impact, including financial loss and reputational damage.
The SOC Workflow
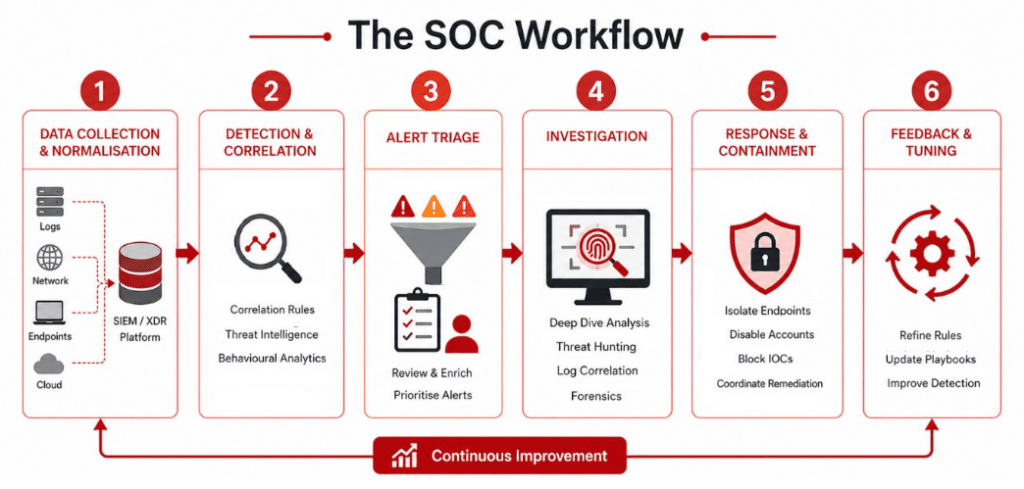
A SOC operates through a structured workflow that converts security data into detection and response actions, spanning stages from data ingestion to continuous improvement.
- Data collection and normalisation: The SOC ingests logs, network flows, endpoint telemetry, and cloud data into central platforms such as SIEM or XDR. The data is aggregated, normalised, and indexed to enable consistent analysis across systems.
- Detection and correlation: Detection is driven by correlation rules, threat intelligence, and behavioural analytics. Many SOCs align detection with frameworks such as MITRE ATT&CK to identify techniques like suspicious command execution or abnormal remote access patterns. Tools such as SIEM, XDR, and UEBA are used to surface anomalies in real time.
- Alert triage: Analysts review alerts and enrich them with context, including user activity, asset criticality, and historical behaviour. The objective is to filter false positives and prioritise incidents for further investigation.
- Investigation: Validated alerts are examined in depth to determine scope and impact. This may involve threat hunting, log correlation, and forensic analysis across endpoints and systems to reconstruct the attack path.
- Response and containment: Once confirmed, the SOC initiates response actions such as isolating endpoints, disabling compromised accounts, blocking indicators of compromise (IOCs), and coordinating remediation with IT teams to minimise disruption.
- Feedback and tuning: After an incident is resolved, detection rules, correlation logic, and playbooks are refined. This continuous tuning improves detection accuracy and reduces future response time.
Each stage depends on the quality of the previous one. Incomplete data collection weakens detection, and ineffective triage increases the risk of missing genuine threats.
Core Technologies Supporting SOC Operations
SOC operations rely on integrated technologies that enable data collection, detection, and response across the environment. These systems work together to provide visibility and execution capability.
- Security Information and Event Management (SIEM) acts as the central data and correlation layer of the SOC. It handles log ingestion, aggregation, and correlation across systems, forming the foundation for detection, analysis, and investigation.
- Extended Detection and Response (XDR) extends visibility across endpoints, networks, and cloud environments, enabling coordinated detection and response from a unified interface.
- Endpoint Detection and Response (EDR) provides deep visibility at the endpoint level, allowing analysts to detect, investigate, and remediate threats directly on affected systems.
Threat Intelligence Platforms enrich detection with external context, including indicators of compromise (IOCs), indicators of attack (IOAs), and emerging threat patterns.
Roles and Responsibilities of the SOC Team
A SOC operates continuously, as threats do not follow business hours. Most organisations use a shift-based model to maintain uninterrupted monitoring and response capability.
SOC teams are structured to support detection, investigation, and response across different levels of complexity.
- SOC Manager: Oversees operations, sets priorities, and ensures alignment with organisational risk and security objectives. This role also coordinates with executive leadership, including the CISO.
- Security Analysts (Levels 1–3): SOC analysts are structured into tiers based on responsibility and depth of analysis.
- Level 1 (L1): Performs initial monitoring and alert triage, filters false positives, and escalates confirmed incidents.
- Level 2 (L2): Conducts in-depth investigation, correlates events, and determines the scope and impact of threats.
- Level 3 (L3): Focuses on advanced threat detection and response, including threat hunting, detection engineering, and handling sophisticated attacks.
- Threat Hunters: Proactively search for adversaries that evade automated detection, using behavioural analysis and hypothesis-driven investigation.
- Security Engineers: Design and maintain the SOC’s detection and monitoring infrastructure, ensuring tools and integrations function effectively across the environment.
- Forensic and Incident Response Specialists: Lead detailed investigations and coordinate response efforts during significant incidents, including evidence collection and post-incident analysis.
In larger environments, these responsibilities are often further specialised, with dedicated roles for incident response leadership and cross-functional coordination.
SOC vs NOC
A Security Operations Center (SOC) and a Network Operations Center (NOC) serve distinct but complementary roles within enterprise IT.
A SOC is responsible for cybersecurity operations, focusing on monitoring, detecting, analysing, and responding to threats across the organisation’s environment. Its outputs include incident response actions, threat intelligence, and security reporting.
A NOC is the operational hub for network performance and availability. It monitors network and server infrastructure, and ensures uptime through continuous oversight and troubleshooting. Its outputs include performance reports, incident resolution records, and change management logs.
In simple terms, the NOC ensures systems remain available, while the SOC ensures they remain secure.
Types of SOC Operating Models
Organisations typically adopt one of three SOC models, depending on scale, budget, and in-house capability:
- In-house SOC: The organisation builds and operates its own SOC. This provides full control, deeper alignment with business context, and the ability to develop customised detection and response processes. However, it requires significant investment in tooling, infrastructure, and skilled personnel, along with the complexity of maintaining 24/7 operations.
- Managed Detection & Response (MDR)/ SOC-as-a-Service: Security operations are outsourced to a managed provider. This model enables faster deployment, predictable costs, and access to experienced analysts with continuous coverage. It reduces the burden of staffing and operations but may limit customisation and create dependency on the provider’s processes and tooling.
- Hybrid Model: A combination of in-house and managed services. Typically, internal teams retain control over strategy, high-priority investigations, and environment- specific tuning, while external providers handle continuous monitoring and initial triage. This approach offers flexibility and scalability but requires clear responsibilities, integration, and communication between teams.
Each model involves trade-offs between control, cost, speed of deployment, and operational maturity. In practice, many organisations adopt managed SOC-as-a-service to achieve faster deployment and continuous coverage without the overhead of building and maintaining in- house capabilities.
Traditional vs Modern SOC
| Capability Area | Traditional SOC | Modern SOC |
| Approach | Reactive, responding after alerts are triggered | Proactive, driven by threat hunting and continuous threat monitoring |
| Detection Model | Rule-based, heavily reliant on SIEM correlation | Intelligence-driven, combining threat intelligence, behavioural analytics, and frameworks such as MITRE ATT&CK |
| Tooling Architecture | Disconnected tools operating in silos | Integrated platforms (XDR, cloud SIEM) with unified visibility |
| Alert Management | High alert volume with frequent false positives | Prioritised, context-rich alerts with reduced noise |
| Workflow | Manual enrichment and investigation | Automated enrichment and orchestration using SOAR and AI |
Role of AI in Modern SOC Operations
Artificial intelligence is reshaping SOC operations by improving speed, scale, and consistency. Its role is not to replace analysts, but to enhance their capabilities.
| Area | Impact of AI in SOC |
| Detection and triage | Analyses large volumes of telemetry to identify patterns, prioritise alerts, and surface high-risk activity earlier |
| Automation (Level 1 tasks) | Automates repetitive tasks such as alert triage, enrichment, and initial response, reducing analyst workload and response time |
| Decision support | Provides contextual insights that support faster and more informed investigation and response decisions |
| Role evolution | Shifts analysts’ focus on threat hunting, detection engineering, and incident strategy rather than repetitive analysis |
AI enables faster detection and response, but effective SOC operations still depend on human judgement for complex investigations and decision-making.
Benefits of a SOC
Beyond its ability to reduce detection and response time, a well-functioning SOC delivers several operational and business advantages:
- Reduced operational disruption: Faster detection and coordinated response minimise downtime and allow internal teams to remain focused on core business functions.
- Improved business continuity: By identifying and containing threats early, a SOC helps maintain stable operations and prevents incidents from escalating into major outages.
- Enhanced incident response: Structured workflows and defined playbooks enable faster, more consistent handling of security incidents.
- Proactive threat detection: Continuous monitoring improves the organisation’s ability to detect emerging threats before they result in material impact.
- Increased stakeholder confidence: Demonstrating continuous security operations helps maintain trust with customers, partners, and regulators.
SOC Compliance, Auditing, and Trust
1. The difference between SOC and SOC 1, SOC 2, SOC 3
The term “SOC” is used in two different contexts. A Security Operations Center (SOC) refers to a cybersecurity function responsible for monitoring and responding to threats. In contrast, SOC 1, SOC 2, and SOC 3 reports are audit frameworks developed by the AICPA to evaluate an organisation’s control environment.
These reports help organisations demonstrate that appropriate controls are in place whether for financial reporting integrity (SOC 1) or broader data and system protection (SOC 2/SOC 3).
2. SOC 1, SOC 2, SOC 3 Explained
- SOC 1: Focuses on controls relevant to financial reporting, particularly for organisations that impact client financial systems.
- SOC 2: Evaluates security controls based on trust service criteria such as security, availability, confidentiality, processing integrity, and privacy.
- SOC 3: A simplified, public-facing version of SOC 2 designed for general distribution without detailed control disclosures.
3. Compliance Frameworks in SOC Environments
Security operations also align with broader compliance principles, including:
- People, Process, Technology alignment: Ensuring security is embedded across organisational structure, workflows, and systems
- Data protection principles: Including lawfulness, minimisation, accuracy, retention control, and confidentiality safeguards
Optimising SOC Operations: Key Practices
A SOC’s effectiveness is not defined by tools alone, but by how consistently it executes core operational practices.
- Align detection with business context: Detection and response should be prioritised based on asset criticality, business impact, and risk exposure. This ensures that analyst effort is focused on what matters most, rather than treating all alerts equally.
- Continuously integrate threat intelligence: External threat intelligence must be operationalised, not just consumed. Indicators, tactics, and emerging attack patterns should be regularly incorporated into detection logic and playbooks.
- Apply automation selectively: Automation is most effective when applied to repetitive, high-volume tasks such as alert enrichment and initial triage. Over-automation without context can introduce blind spots; the objective is efficiency without loss of control.
- Maintain visibility across hybrid environments: As organisations operate across on-premises, cloud, and SaaS environments, consistent telemetry collection and correlation are critical. Gaps in visibility remain one of the most common causes of missed detection.
- Continuously tune and improve detections: Detection logic requires ongoing refinement based on incident learnings, false positives, and evolving threat behaviour.
A static SOC degrades quickly; continuous tuning is essential for maintaining relevance.
24/7 SOC Coverage with Anzen
Cyber threats operate continuously, waiting for the perfect opportunity to attack and exploit your vulnerabilities, making round-the-clock monitoring and incident response a core requirement for modern security operations.
Organisations typically choose between building an in-house SOC or adopting a Managed SOC or SOC-as-a-Service model to reduce operational complexity while maintaining security maturity.
Anzen provides a managed SOC service for continuous 24/7 x 365 monitoring, threat detection, and incident response without the adjoining risk and resources required to build, sustain, and appropriately staff an internal SOC.
By combining AI-driven alert prioritisation with a technical analyst’s manual validation, Anzen reduces false-positives and surfaces only true incidents, enabling faster response and containment within operational timelines.
Reality Check for CISOs
A SOC delivers value only when it is properly executed, continuously tuned, and correctly instrumented. The presence of tools alone does not equate to security coverage.
Visibility gaps, misconfigured telemetry, and incomplete log ingestion can create blind spots that attackers actively exploit. In such cases, even well-funded environments experience delayed detection and extended dwell time.
Ultimately, SOC performance is determined by execution: the quality of telemetry, the speed of detection, and the consistency of response. Weakness in any of these areas directly increases exposure and amplifies breach impact.
A SOC should therefore be treated as a continuously operating risk control function, not a static security layer or toolset. Its effectiveness is defined by how reliably it reduces detection time and limits operational impact under real attack conditions.
FAQs
What does a Security Operations Center (SOC) do?
A Security Operations Center (SOC) continuously monitors, detects, investigates, and responds to cybersecurity threats using SIEM, XDR, DLP, and other tools to maintain visibility, identify suspicious activity, and reduce risk.
What are the four key functions of a SOC?
The four core functions of a SOC are to Monitor, Detect, Analyse, and Respond. These form a continuous cycle to track threats, investigate activity, and execute incident response, maintaining visibility and reducing risk.
Is a SOC a 24/7 operation?
A SOC may operate 8/7, 16/7, or 24/7, but continuous 24/7 monitoring, alert triage, and incident response provide stronger coverage, reducing attacker dwell time and limiting breach impact.
What is the difference between a SOC and a NOC?
A SOC focuses on cybersecurity, detecting and responding to threats like malware, phishing, and breaches, while a NOC manages network performance, availability, and uptime. They serve different, complementary functions.
What is SOC 2 and is it mandatory in India?
SOC 2 is an auditing framework developed by the American Institute of Certified Public Accountants (AICPA) that evaluates an organization’s controls related to security, availability, and confidentiality. It is not legally mandatory in India, but many global clients require SOC 2 compliance as part of vendor risk and data protection requirements.
Where do most cyberattacks begin?
Most cyberattacks begin with phishing or credential-based attacks, where users are tricked into revealing login details, enabling initial access, privilege escalation, lateral movement, and potential compromise without continuous monitoring.
What are the most common types of cyber security threats?
Common cyber threats include malware (ransomware, viruses), phishing and social engineering, man-in-the-middle (MitM) attacks, and denial-of-service (DoS) attacks targeting systems, networks, and users to steal data or disrupt operations.
What technologies are used in a SOC?
A SOC uses SIEM, XDR, EDR, and threat intelligence platforms to collect and correlate data, detect threats in real time, support investigation, and enable coordinated incident response.
What is the role of SIEM in a SOC?
SIEM acts as the central data and correlation layer in a SOC, aggregating logs, normalizing and analysing data, detecting suspicious activity, and supporting investigation, compliance, and audit-ready reporting.
Can AI replace SOC analysts?
AI cannot replace SOC analysts but empowers them by automating alert triage, data enrichment, and pattern detection, enabling focus on investigations and decision-making while improving speed, accuracy, and efficiency.
What is SOC 1, SOC 2, and SOC 3?
SOC 1, SOC 2, and SOC 3 are audit reports developed by the American Institute of Certified Public Accountants to evaluate an organisation’s internal controls.
1. SOC 1 focuses on controls relevant to financial reporting.
2. SOC 2 assesses controls based on trust service criteria such as security, availability, and confidentiality.
3. SOC 3 is a simplified, public-facing version of SOC 2.
Together, these reports help organisations demonstrate that appropriate controls are in place whether for financial reporting integrity (SOC 1) or broader data and system protection (SOC 2/SOC 3).
What is a SOC 2 Type 2 audit?
A SOC 2 Type 2 audit is an independent assessment that evaluates the design and operating effectiveness of an organisation’s security controls over a defined period. Unlike a Type 1 report, which is a point-in-time review, Type 2 validates that controls are consistently applied and functioning effectively, making it the more rigorous and widely required standard for service organisations.
Is SOC 2 mandatory in India?
SOC 2 is not legally required in India. However, it is commonly expected by global enterprise clients, particularly in SaaS, cloud services, and outsourced IT environments where assurance over security practices is a procurement requirement.
Who are L1, L2, and L3 SOC analyst?
SOC analysts are structured into tiers based on responsibility and depth of analysis:
1. L1 (Level 1): Performs initial monitoring and alert triage, filters false positives, and escalates confirmed incidents.
2. L2 (Level 2): Conducts in-depth investigation, correlates events, and determines the scope and impact of threats.
3. L3 (Level 3): Focuses on advanced threat detection and response, including threat hunting, detection engineering, and handling sophisticated attacks.
This tiered model ensures efficient handling of security events across increasing levels of complexity.
